The Public Manager Magazine Article
Member Benefit
A New Way of Evaluating Cybersecurity to Reduce Risk
Content
As technology advances and potential adversaries become more capable, cyber attacks pose a growing threat to the security of government information. Unfortunately, current government policies and processes are not measuring activities that address this dynamic threat.
As technology advances and potential adversaries become more capable, cyber attacks pose a growing threat to the security of government information. Unfortunately, current government policies and processes are not measuring activities that address this dynamic threat.
Sun Sep 15 2013

Content
As technology advances and potential adversaries become more capable, cyber attacks pose a growing threat to the security of government information. Unfortunately, current government policies and processes are not measuring activities that address this dynamic threat.
As technology advances and potential adversaries become more capable, cyber attacks pose a growing threat to the security of government information. Unfortunately, current government policies and processes are not measuring activities that address this dynamic threat.
Content
Under the Federal Information Security Management Act of 2002 (FISMA), each federal agency is required to develop, document, and implement an agency-wide program to secure its information systems, including those supported by outside contractors. As part of this program, agencies must identify an acceptable level of risk for their information systems and develop the attendant policies, procedures, and security plans to reduce information security risks to an acceptable level in a cost-effective way. FISMA mandates that inspectors general (IGs) of the various federal departments and agencies perform annual, independent assessments to determine the efficacy of these practices.
Under the Federal Information Security Management Act of 2002 (FISMA), each federal agency is required to develop, document, and implement an agency-wide program to secure its information systems, including those supported by outside contractors. As part of this program, agencies must identify an acceptable level of risk for their information systems and develop the attendant policies, procedures, and security plans to reduce information security risks to an acceptable level in a cost-effective way. FISMA mandates that inspectors general (IGs) of the various federal departments and agencies perform annual, independent assessments to determine the efficacy of these practices.
Content
Unfortunately, the implementation of existing security and privacy assessment policies tends to encourage security officials to spend limited cybersecurity resources on measures that do little to enhance the security of information systems. The federal government's approach to evaluating FISMA compliance relies on process-oriented methods that focus on the completion of checklists rather than on whether agency cybersecurity programs measurably improve the security of federal IT assets.
Unfortunately, the implementation of existing security and privacy assessment policies tends to encourage security officials to spend limited cybersecurity resources on measures that do little to enhance the security of information systems. The federal government's approach to evaluating FISMA compliance relies on process-oriented methods that focus on the completion of checklists rather than on whether agency cybersecurity programs measurably improve the security of federal IT assets.
Content
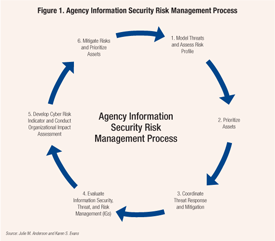
The Organization Cyber Risk Management Framework offers a different approach to cybersecurity evaluation and risk reduction. The framework is designed to foster continuous feedback among agency leaders, IGs, and other oversight organizations. When agencies implement the framework concept, it will illustrate the overall community risk imposed or reduced by a particular agency or department.
The Organization Cyber Risk Management Framework offers a different approach to cybersecurity evaluation and risk reduction. The framework is designed to foster continuous feedback among agency leaders, IGs, and other oversight organizations. When agencies implement the framework concept, it will illustrate the overall community risk imposed or reduced by a particular agency or department.
Content
It does this by linking the central features of any comprehensive cybersecurity strategy (agency threat assessments, risk mitigation action plans, information security management, and recommendations from IG information security evaluations) to agency cybersecurity investments and strategy management. The changes encourage agency leaders to evaluate their risk profiles based on enterprise information holdings rather than according to information systems. In doing so, it delineates a set of tools for IGs to leverage in providing coherent, actionable, and outcome-oriented recommendations to agency IT leaders.
It does this by linking the central features of any comprehensive cybersecurity strategy (agency threat assessments, risk mitigation action plans, information security management, and recommendations from IG information security evaluations) to agency cybersecurity investments and strategy management. The changes encourage agency leaders to evaluate their risk profiles based on enterprise information holdings rather than according to information systems. In doing so, it delineates a set of tools for IGs to leverage in providing coherent, actionable, and outcome-oriented recommendations to agency IT leaders.
Creating a Cyber Risk Management Framework for Government
Content
The framework integrates agency leader and IG efforts to incorporate information security management into the broader strategic management and budgeting process. In essence, the framework provides IGs a better-defined and more integral role in managing the department or agency's information security, while making FISMA's existing guidance regarding risk management more valuable and effective.
The framework integrates agency leader and IG efforts to incorporate information security management into the broader strategic management and budgeting process. In essence, the framework provides IGs a better-defined and more integral role in managing the department or agency's information security, while making FISMA's existing guidance regarding risk management more valuable and effective.
Content
The framework stresses performance outcomes rather than compliance, which allows agency leaders to prioritize actions and tie information security investment to overall organizational priorities.
The framework stresses performance outcomes rather than compliance, which allows agency leaders to prioritize actions and tie information security investment to overall organizational priorities.
Baseline Practices
Content
Before implementing this approach, agencies must establish and demonstrate that they can manage a cybersecurity and data protection baseline by implementing critical security controls and automated continuous monitoring, diagnostics, and mitigation.
Before implementing this approach, agencies must establish and demonstrate that they can manage a cybersecurity and data protection baseline by implementing critical security controls and automated continuous monitoring, diagnostics, and mitigation.
Content
Once these baseline practices are in place, agencies should develop a clear understanding of the threats they face in their current operating environment, and how those threats could be realized. A strong threat model, which includes an agency's current and future operating environment, is critical to any effective risk management strategy.
Once these baseline practices are in place, agencies should develop a clear understanding of the threats they face in their current operating environment, and how those threats could be realized. A strong threat model, which includes an agency's current and future operating environment, is critical to any effective risk management strategy.
Content
After the threat model is developed and applied, agency leaders should identify key organizational mission priorities and map those priorities to critical assets. Then agencies can determine their desired risk profiles and the appropriate controls required to address those threats.
After the threat model is developed and applied, agency leaders should identify key organizational mission priorities and map those priorities to critical assets. Then agencies can determine their desired risk profiles and the appropriate controls required to address those threats.
Risk Mitigation
Content
In the second phase, IGs will be able to evaluate the maturity of the processes associated with information security, threat mitigation, and risk management based on the department or agency's chosen risk attributes and security controls. The evaluation process will be outcome-oriented, draw on live and scenario-based tests of information systems, and result in a prioritized list of recommendations for risk mitigation. The process intends to facilitate communication within agency management, especially among chief information officers (CIOs) and the IGs, to address the identified deficiencies.
In the second phase, IGs will be able to evaluate the maturity of the processes associated with information security, threat mitigation, and risk management based on the department or agency's chosen risk attributes and security controls. The evaluation process will be outcome-oriented, draw on live and scenario-based tests of information systems, and result in a prioritized list of recommendations for risk mitigation. The process intends to facilitate communication within agency management, especially among chief information officers (CIOs) and the IGs, to address the identified deficiencies.
Content
By aggregating the results of the information security risk management evaluation, IG evaluations will help establish a cyber risk indicator for each agency. Rather than a subjective grade, this indicator would be a number determined by a formula. Agencies and oversight entities (Office of Management and Budget \[OMB\], Department of Homeland Security \[DHS\], General Accountability Office, Congress) can use the indicator to manage risk. The risk indicator will yield an overall picture of the adequacy of the agency's information security controls in the context of mission priorities.
By aggregating the results of the information security risk management evaluation, IG evaluations will help establish a cyber risk indicator for each agency. Rather than a subjective grade, this indicator would be a number determined by a formula. Agencies and oversight entities (Office of Management and Budget \[OMB\], Department of Homeland Security \[DHS\], General Accountability Office, Congress) can use the indicator to manage risk. The risk indicator will yield an overall picture of the adequacy of the agency's information security controls in the context of mission priorities.
Recommendations
Content
To better secure information and improve information security evaluations across government, the authors recommend OMB direct the following policy changes:
To better secure information and improve information security evaluations across government, the authors recommend OMB direct the following policy changes:
Content
IGs should adopt the enhanced risk management framework and submit a FISMA evaluation plan to OMB. The plan should include the methodology by which the IG would evaluate an agency's baseline capabilities, implement diagnostic continuous monitoring, and implement prioritized critical security controls.
IGs should adopt the enhanced risk management framework and submit a FISMA evaluation plan to OMB. The plan should include the methodology by which the IG would evaluate an agency's baseline capabilities, implement diagnostic continuous monitoring, and implement prioritized critical security controls.
Content
The National Institute of Standards (NIST) should include in the cybersecurity executive order guidance the enhanced risk management framework, including the cyber risk indicator concept, to bring an evidence-based and outcome-oriented approach to evaluating information risk management.
The National Institute of Standards (NIST) should include in the cybersecurity executive order guidance the enhanced risk management framework, including the cyber risk indicator concept, to bring an evidence-based and outcome-oriented approach to evaluating information risk management.
Content
NIST, in coordination with DHS, should develop and incorporate a clear threat model as a part of the cybersecurity framework to build a foundation for risk management across agencies. This will allow agency leaders to consistently discern what risks can or cannot be accepted.
NIST, in coordination with DHS, should develop and incorporate a clear threat model as a part of the cybersecurity framework to build a foundation for risk management across agencies. This will allow agency leaders to consistently discern what risks can or cannot be accepted.
Content
IGs should prioritize their findings in accordance with the agency or department's defined risk level, and distinguish between managerial and technical controls.
IGs should prioritize their findings in accordance with the agency or department's defined risk level, and distinguish between managerial and technical controls.
Content
Agency CIOs should lead the effort to integrate the IGs' findings into overall department or agency strategic mission priorities, processes, and decisions.
Agency CIOs should lead the effort to integrate the IGs' findings into overall department or agency strategic mission priorities, processes, and decisions.
Content
GSA should expand the Federal Risk and Authorization Management Program (FedRAMP) beyond cloud services. FedRAMP's governance process program, combined with the use of independent third-party assessment organizations (3PAOs), provides a consistent, transparent methodology with established technical controls that both the government and potential contractors understand. The 3PAOs or an equivalent entity should conduct the actual testing of the departments and agencies' operational security controls and provide the results to the IGs for inclusion in their evaluations.
GSA should expand the Federal Risk and Authorization Management Program (FedRAMP) beyond cloud services. FedRAMP's governance process program, combined with the use of independent third-party assessment organizations (3PAOs), provides a consistent, transparent methodology with established technical controls that both the government and potential contractors understand. The 3PAOs or an equivalent entity should conduct the actual testing of the departments and agencies' operational security controls and provide the results to the IGs for inclusion in their evaluations.
Content
Agency leaders can support this effort by leading development of relevant performance measures and standard templates. Multi-dimensional, consistent performance measures should leverage models from the past and combine attributes that allow for measurement and flexibility within and among departments and agencies.
Agency leaders can support this effort by leading development of relevant performance measures and standard templates. Multi-dimensional, consistent performance measures should leverage models from the past and combine attributes that allow for measurement and flexibility within and among departments and agencies.
Content
For example, the existing FedRAMP can be expanded to include the baseline capabilities of agencies in deploying services. FedRAMP determines the technical controls for both low and moderate security levels for cloud providers. It also developed the standard templates and described the data needed to demonstrate the capability.
For example, the existing FedRAMP can be expanded to include the baseline capabilities of agencies in deploying services. FedRAMP determines the technical controls for both low and moderate security levels for cloud providers. It also developed the standard templates and described the data needed to demonstrate the capability.
Content
Implementing the framework will be more successful through the creation and use of standard templates. Data that is gathered consistently according to standard templates is more valuable by virtue of being clearer, more reliable, and more easily compared with other data. Consistent, standardized methods for oversight help resolve conflicts between CIOs and IGs over how to evaluate organizational risk.
Implementing the framework will be more successful through the creation and use of standard templates. Data that is gathered consistently according to standard templates is more valuable by virtue of being clearer, more reliable, and more easily compared with other data. Consistent, standardized methods for oversight help resolve conflicts between CIOs and IGs over how to evaluate organizational risk.
Implementation Challenges
Content
Several key challenges exist in implementing this approach. First, the framework will require different skill sets from IG and CIO staff. The new approach also will raise questions of cost.
Several key challenges exist in implementing this approach. First, the framework will require different skill sets from IG and CIO staff. The new approach also will raise questions of cost.
Content
OMB must offer an explicit tradeoff in its FISMA evaluation guidance about what activities IGs can de-emphasize to reallocate resources to implementing a new framework.
OMB must offer an explicit tradeoff in its FISMA evaluation guidance about what activities IGs can de-emphasize to reallocate resources to implementing a new framework.
Content
In addition, this transition will require changes to existing guidance and IG FISMA evaluation procedures. Perhaps most notably, it demands a shift in strategic emphasis from complying with annual FISMA guidance to improving how agencies manage information security risks on a continual, rather than annual, basis. Due to the technical tests of systems performance, IGs are critical to implementing the prioritized, outcome-oriented assessment.
In addition, this transition will require changes to existing guidance and IG FISMA evaluation procedures. Perhaps most notably, it demands a shift in strategic emphasis from complying with annual FISMA guidance to improving how agencies manage information security risks on a continual, rather than annual, basis. Due to the technical tests of systems performance, IGs are critical to implementing the prioritized, outcome-oriented assessment.
Content
Finally, the success of this framework also depends on the ability and willingness of agencies to empower IT leaders in investment and strategic planning decisions. To achieve a closer link between agency investment, planning, and information security risk management, CIOs must be more integrated into department or agency leadership.
Finally, the success of this framework also depends on the ability and willingness of agencies to empower IT leaders in investment and strategic planning decisions. To achieve a closer link between agency investment, planning, and information security risk management, CIOs must be more integrated into department or agency leadership.
Content
Policy and guidance should clearly communicate each of these values, as well as identify clear milestones to guide the development and implementation of the technical elements of the framework.
Policy and guidance should clearly communicate each of these values, as well as identify clear milestones to guide the development and implementation of the technical elements of the framework.
Content
To fix the problems of today without losing sight of the future, government should implement a more consistent method of evaluation—one that is measurable, transparent, and outcome-oriented.
To fix the problems of today without losing sight of the future, government should implement a more consistent method of evaluation—one that is measurable, transparent, and outcome-oriented.
Content
As long as policy guidance and evaluation methods fail to assess what security and data protection mechanisms significantly reduce risk, government will continue to spend scarce taxpayer resources doing the wrong things.
As long as policy guidance and evaluation methods fail to assess what security and data protection mechanisms significantly reduce risk, government will continue to spend scarce taxpayer resources doing the wrong things.
Content
[
[
Content
Agencies are mandated to assess information systems security risks. Managing those risks on a continual, rather than annual, basis can save scarce resources.
Agencies are mandated to assess information systems security risks. Managing those risks on a continual, rather than annual, basis can save scarce resources.
Content
]( http://files.astd.org/TPM-Article-Images/2013/fall/andersonSB1-L.png )
](http://files.astd.org/TPM-Article-Images/2013/fall/andersonSB1-L.png)
